DMVPN VPN
DMVPN (Dynamic Multipoint VPN) is a Cisco-designed hub-and-spoke VPN architecture that enables the dynamic creation of direct spoke-to-spoke tunnels, effectively forming an encrypted mesh network. It simplifies large-scale deployments by combining multipoint GRE (mGRE) tunnels for data transport with the Next Hop Resolution Protocol (NHRP) to map physical IP addresses to logical tunnel addresses dynamically. This allows spokes to register with a central hub and discover the public IP addresses of other spokes on demand, enabling them to establish direct, secure IPsec tunnels without requiring static configuration for every peer. DMVPN significantly reduces configuration complexity, enhances scalability, and supports dynamic routing protocols. It is primarily used in enterprise WANs to connect numerous branch offices in a flexible and efficient manner.
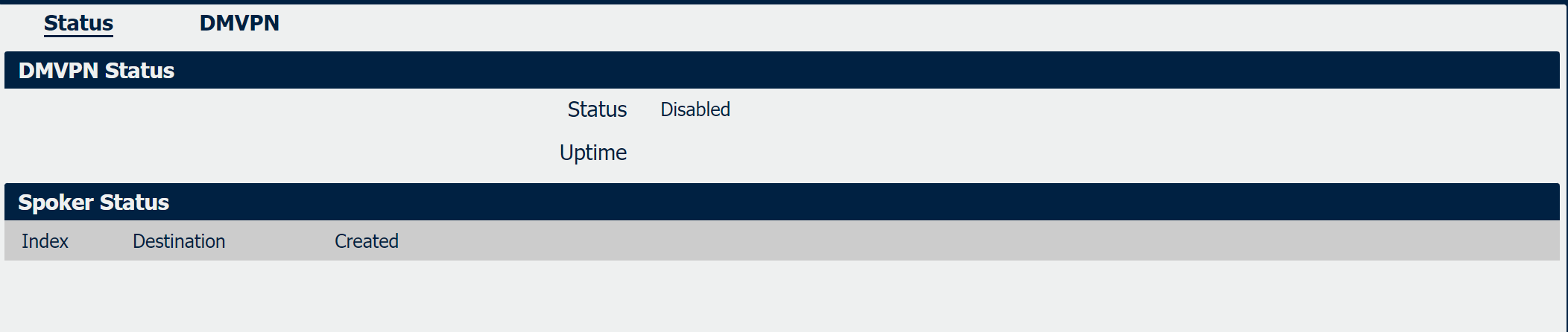
DMVPN Status
|
Field |
Description |
| Status | Display the status of the DMVPN connection. |
| Uptime | Display the uptime of the DMVPN connection. |
Spoke Status
|
Field |
Decription |
| Destination | Display the remote address of the DMVPN Hub. |
| Created | Display the status of the DMVPN Spoker. |
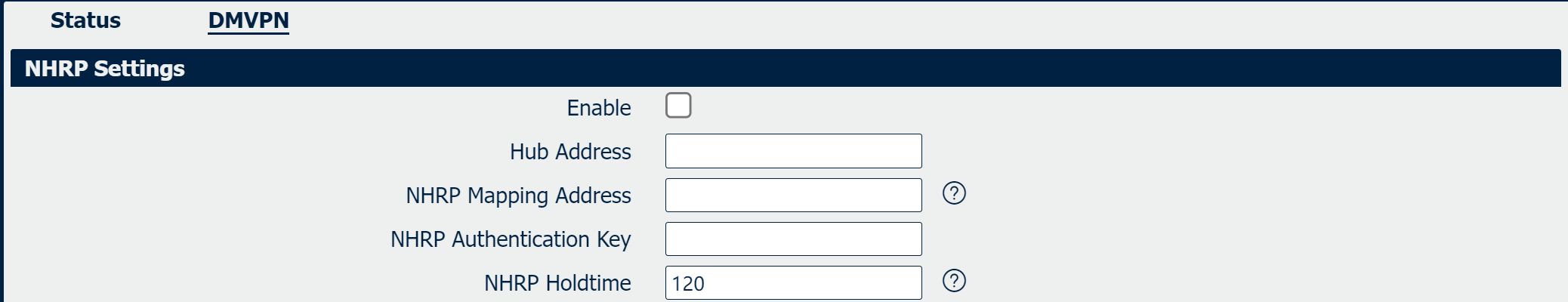
|
Field |
Description |
|
Enable |
Check the option to active DMVPN Service. |
| NHRP Mapping Address | Specify the Local IP for DMVPN Service. |
| NHRP Authentication | Specify the start IP address to be obtained for the DMVPN clients. |
| NHRP Holdtime | Specify the end IP address to be obtained for the DMVPN clients. |
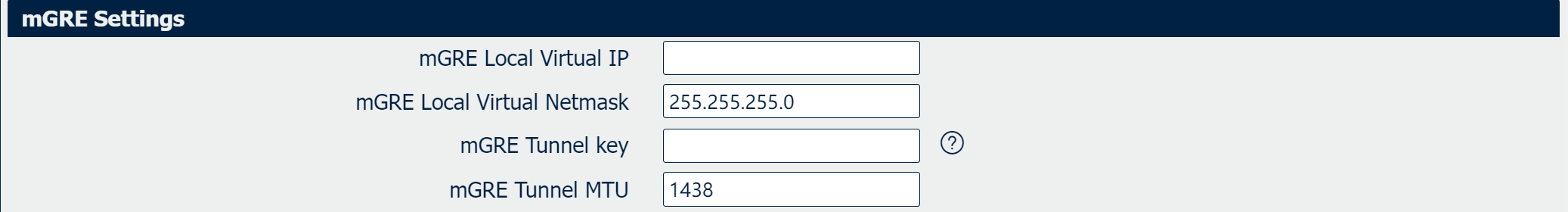
|
Field |
Description |
| Mgre local Virtual IP | Select the authentication type, available options are “CHAP”, “PAP”, “MSCHAP_v1”, “MSCHAP_v2” and “None” |
| mGRE Local Virtual Netmask | Enter the username for authentication |
| mGRE Tunnel Key | Enter the password for authentication |
| mGRE Tunnel MTU | Maximum Transmission Unit, maximum packet size allowed to be transmitted for DMVPN connection. Should be left as default value of 1500 in most cases. |
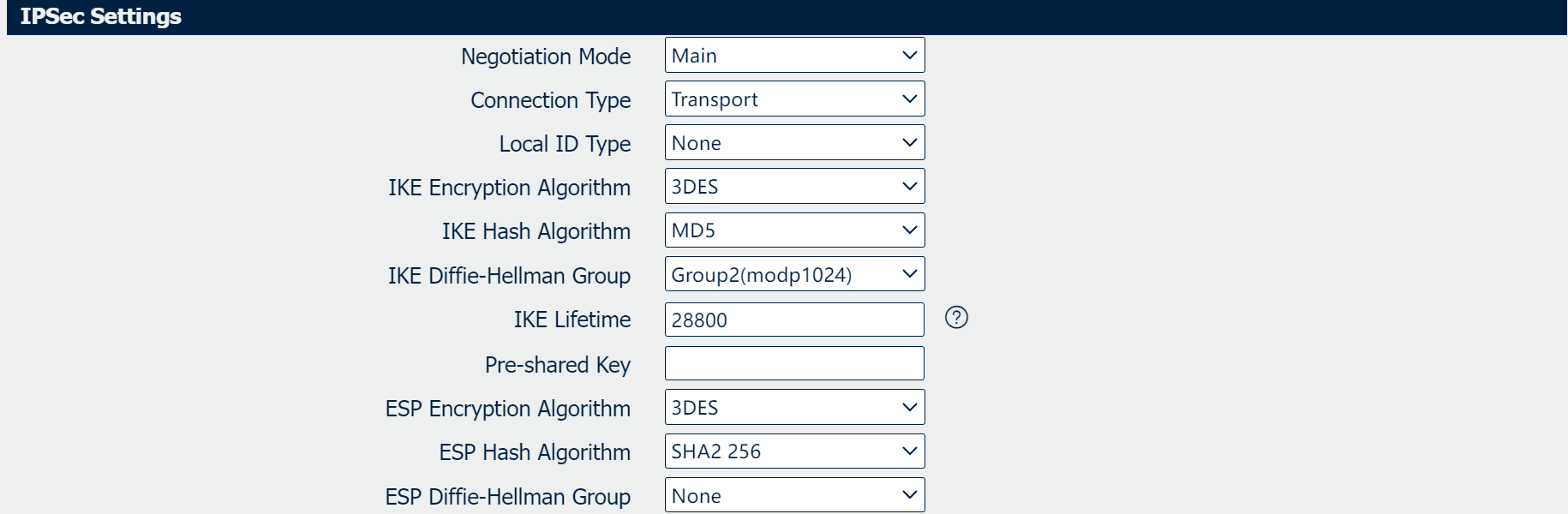
|
Field |
Description |
| Negotiation Mode |
Specifies the negotiation method for establishing the IPsec Security Association (SA). Main Mode provides identity protection, while Aggressive Mode offers faster negotiation at the cost of some security.
|
| Connection Type |
Coonnection types include "Tunnel" and "Transport".
|
| Local ID Type |
Specifies the format of the identifier used by the local gateway during IKE (Internet Key Exchange) phase 1 negotiation. Common types include "IP Address", "FQDN" (Fully Qualified Domain Name) and "User-FQDN(Email address)"
|
| IKE Encryption Algorithm |
Selects the symmetric encryption algorithm used to protect IKE phase 1 negotiations. Include DES, 3DES, AES-128, AES-192 and AES-256, with stronger algorithms requiring more computational resources.
|
| IKE Hash Algorithm |
Selects the cryptographic hash function used for data integrity and authentication within IKE phase 1. Common options are MD5, SHA1, SHA2-128 and SHA2-256.
|
| IKE Diffie-Hellman Group |
Determines the strength of the key exchange used in IKE phase 1. Higher group numbers (e.g., Group 1, 2, 5, 14, 15, 16,17,18) provide stronger security through longer prime numbers but increase computational overhead.
|
|
IKE Lifttime |
Sets the duration, in seconds, for which the Phase 1 Security Association (IKE SA) remains valid before it must be renegotiated. The default value is commonly 86400 seconds (24 hours).
|
|
Pre-shared Key |
A shared secret string used for mutual authentication between VPN peers during IKE phase 1. This is a critical security parameter and must be identical on all configured peers.
|
| ESP Encryption Algorithm |
Selects the encryption algorithm used by the Encapsulating Security Payload (ESP) protocol to provide confidentiality for data traffic within the IPsec tunnel. Examples are DES, 3DES, AES-128, AES-192 and AES-256.
|
| ESP Hash Algorithm |
Selects the integrity algorithm used by the ESP protocol for data authentication within the IPsec tunnel. Options include MD5, SHA1, SHA2-128 and SHA2-256. (though SHA-1 is considered weak).
|
| ESP Diffie-Hellman Group |
onfigures the use of Perfect Forward Secrecy (PFS) for Phase 2 IPsec Security Associations. Enabling PFS (by selecting a DH Group like 1, 2, 5, 14, 15, 16,17,18)) ensures a separate key exchange, enhancing security but potentially increasing connection setup time.
|
| ESP Lifetime | Defines the lifetime of the Phase 2 IPsec Security Association (SA), which governs the encrypted data tunnel. It can be specified in seconds (time) or kilobytes (data volume). When either limit is reached, the SA expires and must be renegotiated (rekeyed) to ensure ongoing security. Common defaults are 28800 seconds (8 hours) and 4608000 kilobytes. |